CipherForge delivers formally verified post-quantum cryptography through a clean API, so your team can migrate to ML-KEM, ML-DSA, and HQC without rebuilding your infrastructure or trusting a black box.
No algorithm lock-in. No key escrow. No foreign dependencies.
Algorithms evolve. Standards shift. CipherForge's orchestration layer lets you swap cryptographic primitives as configuration changes, not infrastructure replacements. When the next standard lands, your system updates without a migration project.

Secret-handling routines are written in Jasmin, a language that enforces constant-time execution and enables formal proof at the assembly level. The vulnerabilities that affected Signal, AWS, and Cloudflare's PQC libraries cannot occur in CipherForge by construction.
CipherForge never stores your encryption keys. Not in transit, not at rest, not ever. Full BYOK across all deployment models. Air-gapped deployment with source code handover available for environments where no external dependency is acceptable.
83% of cryptographic vulnerabilities are implementation failures, not algorithm flaws. CipherForge is architected to close that gap permanently.
Every routine that touches secret values is written in Jasmin, a language that proves constant-time execution at the assembly level by construction. Standard C compilers can silently reintroduce timing side-channels even into correctly-written code. Jasmin eliminates that class of vulnerability entirely, not by convention but by proof.

API-Orchestrated PQC
For organizations needing full control of their encryption, ExeQuantum provides API-driven post-quantum cryptography. Hybrid TLS combines new quantum-safe algorithms with proven classical methods, so you can deploy across languages, frameworks, and layers without disruption.

Pre-Shared Key Mode
In environments where continuous key exchange is impractical, ExeQuantum offers a pre-shared key mode. This reduces handshake delays and dependence on TLS, making it ideal for embedded systems, IoT devices, drones, and other critical infrastructure with tight resource limits.

Isolated Deployment
For maximum sovereignty, ExeQuantum enables fully isolated deployments, including optional code handover. Your team can license optimized source or compiled code (Python, C, Jasmin), integrate it directly, and operate independently, with ongoing engineering support for high-sensitivity use cases.
NIST-standardized ML-DSA, ML-KEM
Zero-trust integration
Cutting edge algorithms such as
HQC and SLH-DSA
Regulatory compliance support
24/7 technical assistance
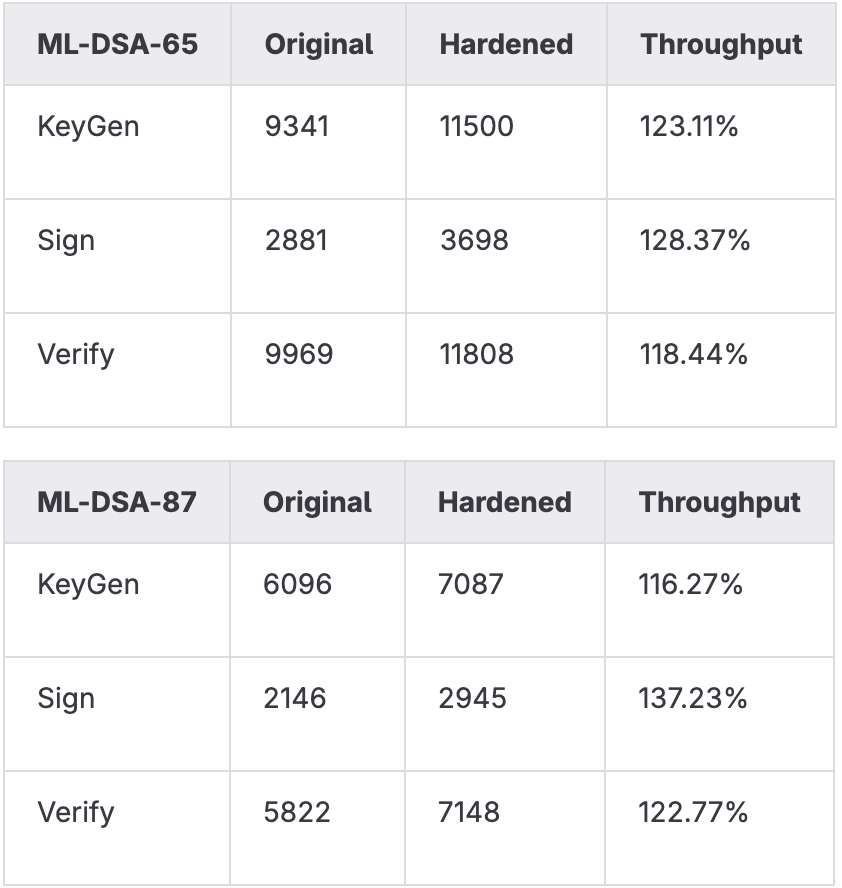
Self-proving and performant
Sovereign data control
Ongoing algorithm updates
ISO 27001
NIST FIPS 203 / 204 / 205
CNSA 2.0
APRA CPS 230
ASD ISM 2030
HIPAA
PCI DSS
SOC 2
GDPR
ENISA PQC Guidelines
AUKUS Tech Cooperation
Full cryptographic inventory across various attack surfaces. Migration roadmaps aligned to NIST, ENISA, and ASD mandates. Audit-ready evidence at every stage. Pass the board question before it gets asked.
ISO 27001 certified. Listed in Austrade's national quantum capability report. Air-gapped and sovereign deployments ensure full control over infrastrcture.
2030 PQC mandates across the US, EU, ME, SEA and Oceania are not aspirational. Harvest-now, decrypt-later attacks are happening today. CipherForge provides the board-level evidence that quantum risk is being actively managed
Clean API abstraction, available on all frameworks, languages, and layers. No need to understand cryptography to integrate it correctly. Documentation available on request. Integration in hours, not weeks.

API integration for instant quantum protection
Deployed in real infrastructure
On-premise tools for sovereign control