CipherScout is proprietary ExeQuantum technology. All scanners are designed, engineered, and maintained entirely by ExeQuantum. No third-party discovery tooling is used.
Live PQC hybrid detection
Fleet-level JWT analysis
Email crypto (DKIM · ARC · S/MIME)
Air-gapped & sovereign deployments
Read-only · No private key access
Deep TLS visibility
CipherScout detects whether a server has already deployed post-quantum hybrid key exchange, including the ML-KEM hybrid groups recommended by NIST and IETF, directly from a live TLS session. Most scanners report only protocol version and cipher suite. CipherScout goes a level deeper, surfacing whether the server is already making the transition.
Certificate inventory
CipherScout retrieves and analyses every certificate presented across your estate, including algorithm type, key size, signature method, issuer chain, and expiry, across HTTPS, SMTPS, LDAPS, and any other certificate-presenting service. Each certificate receives a Quantum Health Score reflecting its vulnerability to Shor's algorithm. The output is a complete, prioritised certificate inventory your PKI and infrastructure teams can act on directly.
API authentication layer
APIs authenticate callers using cryptographic mechanisms, such as token signing algorithms, key types, and OIDC configurations that are rarely audited at the cryptographic level. CipherScout analyses the algorithm commitments your APIs make to every relying party, combining JWKS, OIDC metadata, and TLS posture into a composite quantum vulnerability score for each API authentication surface.
SSH infrastructure
Every SSH server advertises public host keys that clients use to verify its identity. If those keys use quantum-vulnerable algorithms, with RSA being the most common, the administrative access path to your entire server estate is exposed. CipherScout connects to SSH endpoints and reads the advertised host key types and fingerprints without authenticating, without interacting beyond the key exchange phase, and without collecting any credentials or session content.
Underscanned surfaces
Email infrastructure carries its own cryptographic footprint, such as signing keys, authentication mechanisms, and transport security. CipherScout assesses the full email cryptographic surface in a single pass, including the signing algorithms protecting outbound mail and the certificate properties of signed messages (i.e. S/MIME). No email content is read - only the encryption used to encrypt it to ensure nobody else can either.
Live, not static
CipherScout connects directly to the user's token database and analyses the entire JWT population in bulk. Algorithm distribution, header injection risk indicators, claim completeness, and worst-case Quantum-Health Score (QHS) across the fleet. The output is a compliance view, not an individual token report.
Data layer coverage
For declared database targets, CipherScout assesses how data is protected in transit and at rest, covering the encryption on the connection itself, the authentication mechanism in use, and replication security. Assessment is scoped strictly to customer-declared systems, keeping the tool within compliance auditing.
Cloud key inventory
CipherScout retrieves key algorithm, rotation status, expiry, and configuration metadata from cloud key management services across major providers and custom private cloud environments. Access is strictly read-only, and no key material is accessed or returned at any point.
Codebase visibility
CipherScout scans customer-supplied source code to identify where classical cryptographic algorithms are used across the codebase, including legacy hash functions, deprecated key types, and hardcoded cryptographic material. Findings pinpoint exact file locations, giving development teams an actionable list rather than a summary.
Hardware
CipherScout can also be deployed on-premise to scan local certificates, keys, and other encryption in devices on the hardware and OS levels. It can be deployed in devices (i.e. Mac) as well as IoT, OT, and air-gapped systems to find and inventory its cryptography.
cbom-output.cdx.json
{
"bomFormat": "CycloneDX",
"specVersion": "1.7",
"components": [{
"type": "cryptographic-asset",
"name": "TLS-endpoint",
"cryptoProperties": {
"assetType": "protocol",
"algorithmProperties": {
"primitive": "key-agreement",
"keyLength": 2048,
"name": "RSA"
}
},
"properties": [{
"name": "qvs-score",
"value": "95" // quantum vulnerable
},{
"name": "quantum-vulnerable",
"value": true
},{
"name": "pqc-hybrid-detected",
"value": false
}]
}]
}Deterministic
Every scan produces a structured findings report telling you exactly which cryptographic assets are quantum-vulnerable, how severe the exposure is, and what you already have right. Generated by a rules engine, not AI, so the output is reproducible, auditable, and defensible in regulated environments.
AI-Assisted
Turn your findings into a migration plan with phases, priorities, and concrete next steps at the push of a button. Built on your CBOM, never on assumptions. The kind of report a CISO takes to the board, and a DevOps team can actually execute.
Getting a migration report shouldn't necessarily mean sending your security data to a third-party AI. With CipherScout, it doesn't have to.
The AI migration report is generated from your CBOM, which is a record of cryptographic configuration, not business data. No credentials, no payloads, no application content. Under CipherScout's standard deployment, ExeQuantum cannot see your CBOM, your findings, or the report you generate. What happens in your environment stays there.
AI processing is disabled unless you enable it. Your findings report, CBOM export, and Quantum Health Scores are all produced without any AI involvement. The migration report is a separate step you opt into. It runs once, on demand, against the CBOM you choose to submit. No background processing, no automatic analysis.
You are not required to use a specific AI provider. If your organisation has an approved AI deployment, be it a managed Azure OpenAI instance, a locally-hosted model, or any other compliant configuration, you can point CipherScout's AI layer at that instead. Your procurement and security policies stay intact.
Governments and standards bodies worldwide are formalising cryptographic inventory requirements. CipherScout's CBOM output is designed to satisfy them.
NIST PQC Standards
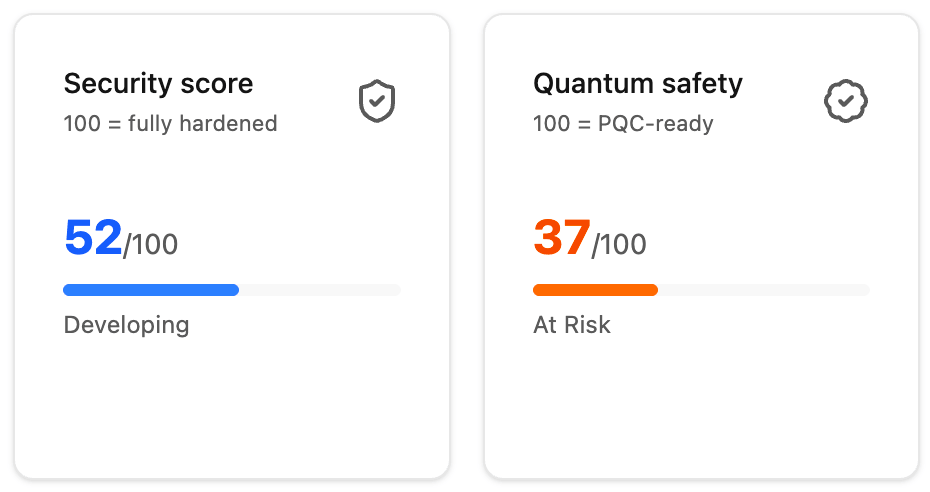
CipherScout automatically benchmarks your entire cryptographic inventory against the finalized NIST Post-Quantum Cryptography standards. Our deterministic engine identifies non-compliant legacy algorithms and validates your fleet's readiness for FIPS 203, 204, and 205. The output is a high-level compliance view that quantifies your transition progress with a unified Quantum-Health Score (QHS).
FIPS 203
FIPS 204
FIPS 205
SP 800-208
SP 800-131A
Financial & Critical Infrastructure
Cryptographic inventory is now an explicit requirement under PCI DSS 4.0 (Requirement 12.3.3). CipherScout's five-surface coverage and CBOM output satisfy the inventory evidence requirement.
PCI DSS 4.0
ISO/IEC 18033
GDPR
ISM
Government & Sovereign Requirements
Air-gapped deployment, data residency controls, and the absence of private key handling make CipherScout suitable for government and critical infrastructure environments subject to ACSC, BSI, and ENISA guidance.
ACSC ISM
BSI (DE)
ENISA
CISA
NACSA
CERT-in
DESC